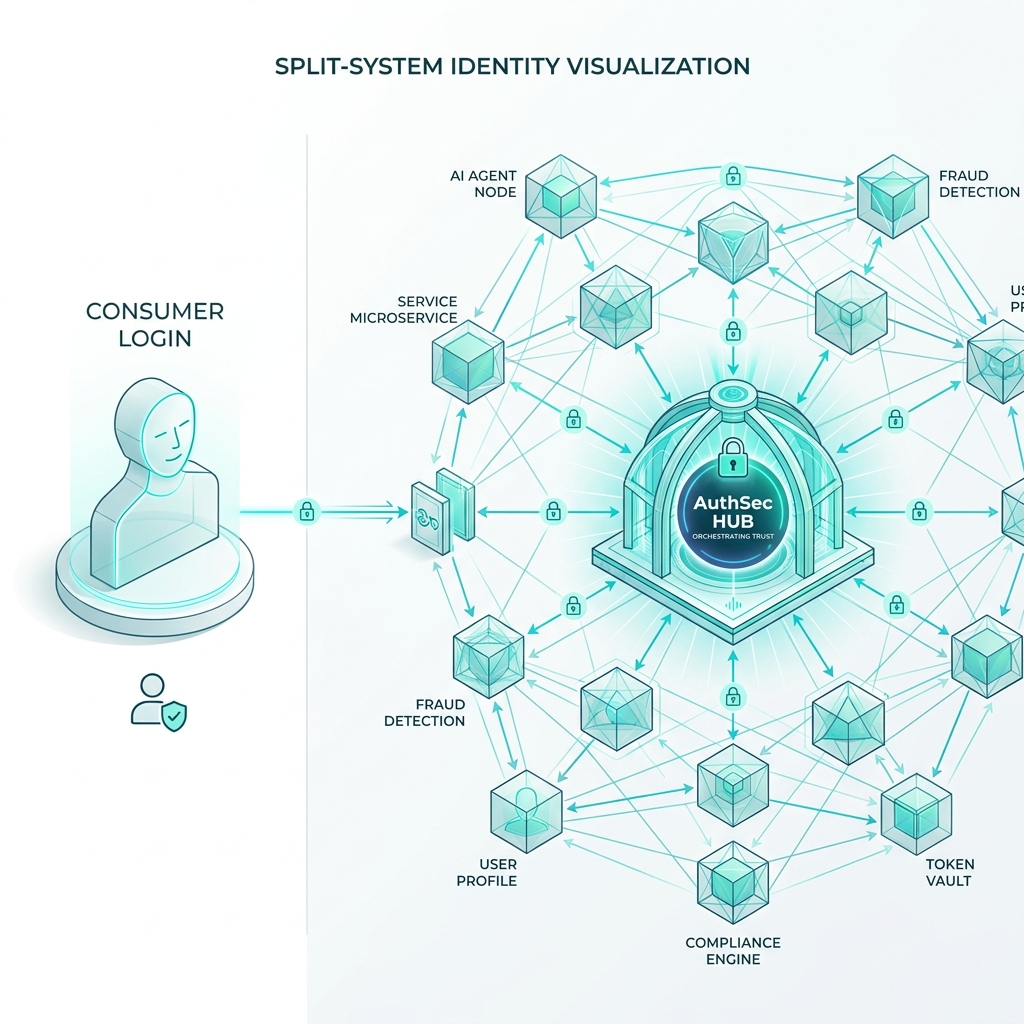
AuthSec vs Stytch: Workload Identity vs Consumer Login
Stytch is excellent for passwordless consumer login. AuthSec is built for what comes next — AI agents that need their own identity, trust delegation, and workload-native security.
Agent-First Identity
MCP server authentication, SPIFFE workload identity, and headless auth flows for AI agents — native, not hacked on.
Trust Delegation
Let users delegate scoped, least-privilege access to autonomous agents. Short-lived tokens bounded by RBAC role bindings.
Self-Host Everything
Full Apache 2.0 open-source. Deploy on-prem, in your VPC, or air-gapped. Complete data sovereignty.
Architecture-level detail
Deep Technical Comparison
Consumer login toolkit vs. a full-stack identity runtime for humans and machines.
Stytch Approach
The Login UX Kit
Beautiful passwordless login flows — magic links, OTPs, social auth. Optimized for consumer-facing applications.
- ✕Great passwordless UX for end-users
- ✕No trust delegation model
- ✕No workload identity support
AuthSec Approach
The Full Stack Runtime
Auth, RBAC, federation, trust delegation, workload identity, and provisioning — one service, one API.
- ✓MCP + SPIFFE workload identity
- ✓Trust delegation for user-to-agent auth
- ✓Tenant-scoped RBAC + SCIM provisioning
Stytch Enterprise
Limited Enterprise Story
Enterprise SSO and SCIM are available but limited. No deep RBAC, no workload identity, no agent auth flows.
- ✕Limited SCIM 2.0 support
- ✕No device auth or CIBA flows
AuthSec Enterprise
Enterprise-Native
Unlimited SSO, deep SCIM provisioning, device auth, CIBA, voice auth, and Hydra login/consent orchestration.
- ✓Device, CIBA, and voice auth flows
- ✓Hydra login/consent orchestration
- ✓Per-tenant database isolation
Where Stytch hits a wall
Stytch is purpose-built for consumer login. When your product grows into enterprise SSO, AI agents, or workload security, its architecture doesn't stretch.
No Agent Identity
Stytch has no concept of workload identity or MCP server auth. Your AI agents can't authenticate through Stytch.
Trust Delegation Missing
Users can't delegate scoped access to agents. There's no delegated token model — you'd build the entire flow yourself.
No Self-Host Path
Stytch is cloud-only. For regulated environments, air-gapped deployments, or data sovereignty requirements — there's no option.
Enterprise readiness, day one.
All the features you'd typically upgrade for are included from the start.
Enterprise SSO
Unlimited SAML & OIDC connections with zero per-connection pricing.
SOC2 & ISO Ready
Compliance-grade audit logs, encryption at rest, and data residency controls.
MFA & RBAC
Multi-factor auth and role-based access control ship in the free tier.
SIEM & Audit
Stream events to your SIEM. 30-day built-in retention on all tiers.
Predictable Pricing vs. Per-User Scaling.
Stytch's pricing scales per-user and locks enterprise features behind higher tiers. AuthSec ships flat-fee tiers that include all enterprise tooling — SSO, SCIM, MFA, RBAC — on every plan.
100%
Open-source. Self-host, audit, and extend the entire identity platform.
0$
Extra for enterprise features. SSO, SCIM, MFA, and RBAC are free on every plan.
Outgrow consumer login.
Build on an identity runtime that handles humans, agents, and workloads — not just passwordless login screens.